A requirement of access control is that it should be proportional to the risk and impact; be transparent to the users whilst meeting the requirements of the company in terms of compliance.
Increasingly these days technology is being deployed to provide the solutions. Biometric solutions are not always transparent to the user, provide the level of convenience required and can be costly, mechanical locks such as cypher locks are also not transparent enough to the user or convenient and it can be difficult to change keys or codes and distribute the news across an organisation in timely manner, it is not a solution that scales well. A popular solution is the contactless entry card system that is based on Radio Frequency Identification (RFID) or Near Field Communications (NFC) technology. Such systems allow organisations to distribute key cards or tokens to employees and trusted 3rd parties and individual credentials can be revoked without affecting the whole population of users. Being wireless based the cards or tokens only need to be in proximity to the reader provider high levels of convenience whilst provider unique identification and accountability with entry and potentially exit logging.
Such systems can be easily purchased from eBay, Amazon to various system installers and can vary from individual door locks to enterprise systems. Those systems that rely on wireless communication to provide identification and authentication whilst being convenient and transparent to users are also subject to attack due to the nature of wireless communication being able to be intercepted and some systems being designed in an insecure manner.
Since April 2014 as part of talks that I have been giving to branches of the BCS and at universities and for other organisations we demonstrate attacks on door access control systems.
The demonstration shows 2 types of attackers on the door access system.
- Compromising the door controller
- Attacking the tokens
The door controller was purchased from Amazon and using information obtained by Googling components and other information it was possible to compromise the system in a number of ways.
Compromising the door controller
In this attack physical access to the door controller is required in order for the access codes to be captured. The proximity door controllers have a number of elements.
- RF circuit
- Micro-controller
- Door latch controller
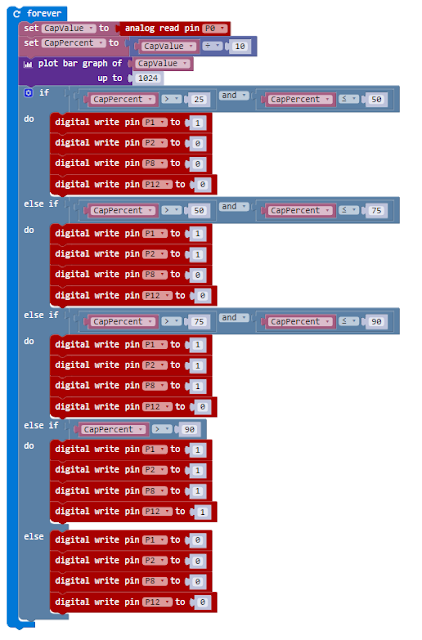
In the attack we demonstrate we intercept the signals from the RF circuit as they are being passed to the Micro-controller allowing us to read and capture authentication codes transmitted to the door controller so that we can then record and replay them back to the controller at a later time or use them in a cloned token.
By soldering some pins to the circuit board it was possible to capture the stream of binary data from the RF circuitry. Initial work was done with an Arduino, however small systems such as the Teensy could be used.
It was possible to capture the codes which could be stored or if a wireless adapter was added to the system they could be transmitted to a nearby laptop.
A small enough device could be attached to a controller and the controller then fitted back on the wall and the compromised controller could be used to capture legitimate users access tokens allowing them to be used in an attack.
Attacking the tokens
Proximity door controllers work by having a microchip connected to a coil, when the coil is moved through a magnetic field it generated a voltage which powers the microchip which then modulates a signal through the coil which can be picked up by the receiver which generated the initial magnetic field.
It is possible using simply electronics and a micro-controller like an Arduino to replicate either the access controller or spoof a token.
In the attack we demo, we do both. A coil, simple electronics and an Arduino are used to simulate an access controller. Any token in range of the spoofed access controller will transmit their codes which can be recorded by the Arduino.
The exactly same circuit can then be used to spoof a token and replay the captured codes back to a genuine door controller allowing a user to be spoofed and the door controller to be tricked into opening. By using a micro-controller board, it can be programmed to use the captured code as a base for a brute force attack on all tokens by transmitting modified codes and seeing if the controller responds.
Conclusion
These are simply attacks that work on unsophisticated controllers; however the principles can be used for more sophisticated attacks that would work on more advanced controllers. Unless a system has been designed with security in mind it is often easy to attack those systems.